Review: SmoothWall Corporate Server 2.0
(c) Richard Drummond 2002-2003. This article may be freely distributed as long as this copyright notice remains attached. Originally published in Linux Format, December, 2002. Prepared for the web May, 2003.
Note: Your browser doesn't support stylesheets, so the layout of this article will be incorrect
With the SOHO market sewn up, this popular firewall looks for bigger fish to fry.
When first released in July 2000, SmoothWall revolutionized the entry-level firewall market by giving users the ability to turn a redundant, low-spec PC into an easy-to-set-up, secure, Linux-based firewall. The original SmoothWall was free software, but the creators soon recognized the commercial value of their product and set up a company to market a commercially-supported version.
The new SmoothWall Corporate Server 2.0, the product on test here, is a whole lot more than just a retail version of the current SmoothWall GPL release, however. It has been expanded and re-targeted at the medium enterprise market. It features more flexible networking tools, support for SCSI disks for the first time, a revamped administration interface, and a new modular and scalable architecture. Corporate Server can be extended with add-on services - such as more powerful VPN functionality and content-filtering - and hence you only pay for services that you need (see the side-bar to the right, Add-on modules). Despite all of this, it remains as easy to use as ever.
Smooth installation
One of the big selling points of SmoothWall is its ease of installation. You simply boot from the install disc, answer a few questions, reboot your machine and - presto! - you have a functional and secure firewall. By default it sets up the firewall rules so that all incoming traffic is blocked and all outgoing traffic is allowed. This policy will work for most, so most users will find that little configuration is required - unlike with some firewall products.
SmoothWall is simplest to install from the bootable CD. If your machine can't boot from CD - this is designed to work on redundant PCs, after all - images are supplied on the CD to create bootable floppies. You can even install on a machine sans CD-ROM drive via a network.
The installer itself is based on the familiar Red Hat text-console, dialog-based system, although this has been vastly simplified and asks you for a minimum of information. After picking the install type - from CD or network - it prompts you that the hard drive is to be repartitioned. SmoothWall takes over an entire disk, deleting any previous contents. It creates root, boot and swap partitions and a /var/log partition for storing log files. SmoothWall now uses the ext3 filesystem throughout, and this - and the separation of log files - should ensure that if your SmoothWall box does go down while writing to the disc, damage will be a minimum and will be quick and easy to recover from.
The next task is network configuration. Like the previous incarnations of SmoothWall, Corporate Server supports three network zones: Green, or the local network; Red, the Internet; and Orange, the DeMilitarized Zone or DMZ. The first step is to set up your Green interface - which must be an Ethernet adapter. SmoothWall can probe for a NIC automatically, or you can manually select a kernel driver to load. You just then need to specify the IP address and netmask for the interface.
Support for a fairly comprehensive range of NICs is included, but, perhaps, this is the only area of SmoothWall that the user will notice or care that SmoothWall is actually based on a 2.2 kernel rather than a more modern 2.4 kernel. The reason: driver support. As an example, my test machine had a recent Acton Technology Tulip-based card, which failed to be automatically detected by SmoothWall and is unsupported by SmoothWall's tulip driver (this card does work with newer 2.4 series kernels, though). To be fair, the vast majority of NICs will work - and, certainly, all the others I tried did. However, the information about precisely what hardware Corporate Server supports isn't available on the SmoothWall web site, although it is included in the documentation on the install disc (this documentation is excellent, by the way).
Configuration of the Red interface is similar if you choose this to be a NIC rather than a dial-up device such as an analog modem or ISDN adapter - although, here, DHCP is supported for determining IP address, etc. PPP over Ethernet is also supported, so you can use a wide variety of routers, cable modems, etc. on your Red interface. If you are using ISDN, SmoothWall can probe for your ISDN adapter - and drivers are included for an impressive range of internal and external devices - or, again, you can load a driver manually. The other option for the Red interface is the Alcatel USB ADSL modem. The connection settings for any kind of dial-up device must be configured from the web interface post-installation.
The rest of the installation is fairly routine. You choose your keyboard layout, hostname and passwords. Usefully, you can also configure SmoothWall's DHCP server here. Another handy feature is that the installer gives you the option of restoring your firewall settings from a back-up floppy, and this will save you a lot of work should you need to re-install.
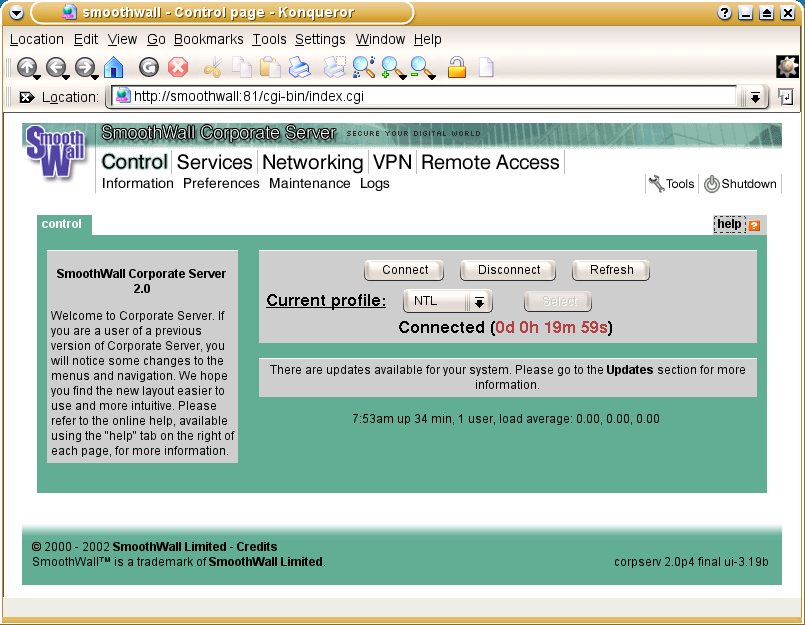
Smooth interface
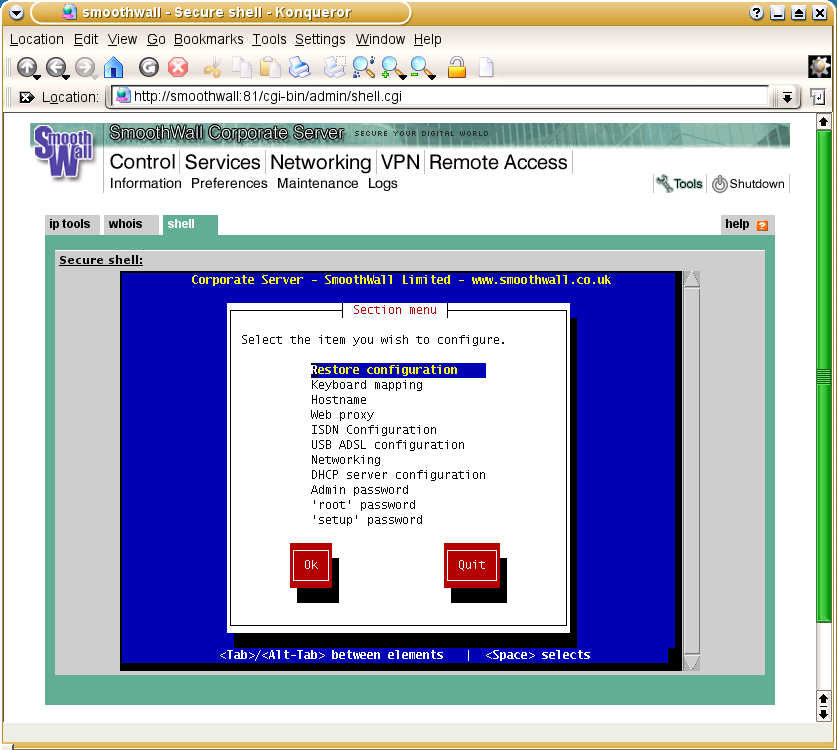
When you boot up your newly-installed SmoothWall machine, you will have a working firewall. A limited amount of configuration can be performed locally, via a dialog-based set-up tool, but most administration will be performed via SmoothWall's web interface. This can be accessed via a web browser pointed at port 81, and a secure connection is also available at port 445. The web interface has been redesigned in Corporate Server, with a more business-like look. The interface is split into eight pages according to task (and most of these are further sub-divided into 'tab panes'), so navigation is easy. Online-help is available on each page.
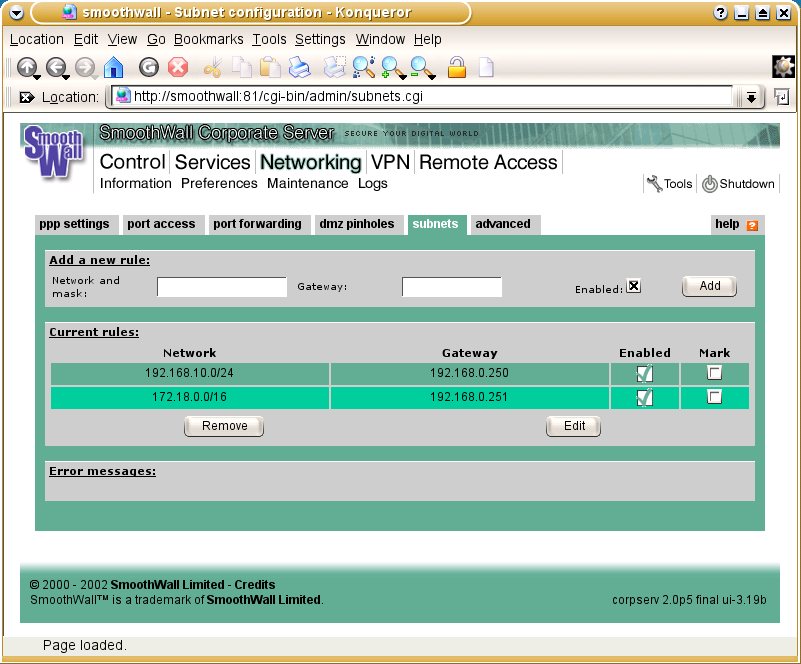
The 'Networking' page is where you can set up your security policy and configure your dial-up connection. Most of this will be familiar from previous SmoothWall releases. The 'Port access' section lets you open up specific ports for incoming traffic to your local network or DMZ; 'Port forwarding' lets you forward incoming connections from a port on the Red interface to a port on a specified host within your DMZ, useful when you only wish to expose a particular service on some host in the DMZ; and 'DMZ pinholes' allows you to open up connections from the DMZ to the Green network, useful if your web server needs access to a database in the local network, say. New in this section is support for multiple sub-nets within the Green network. Here you can define the address ranges of any sub-nets and the IP address of the router via which SmoothWall can access them. This feature allows SmoothWall to protect much more complex local networks than before.
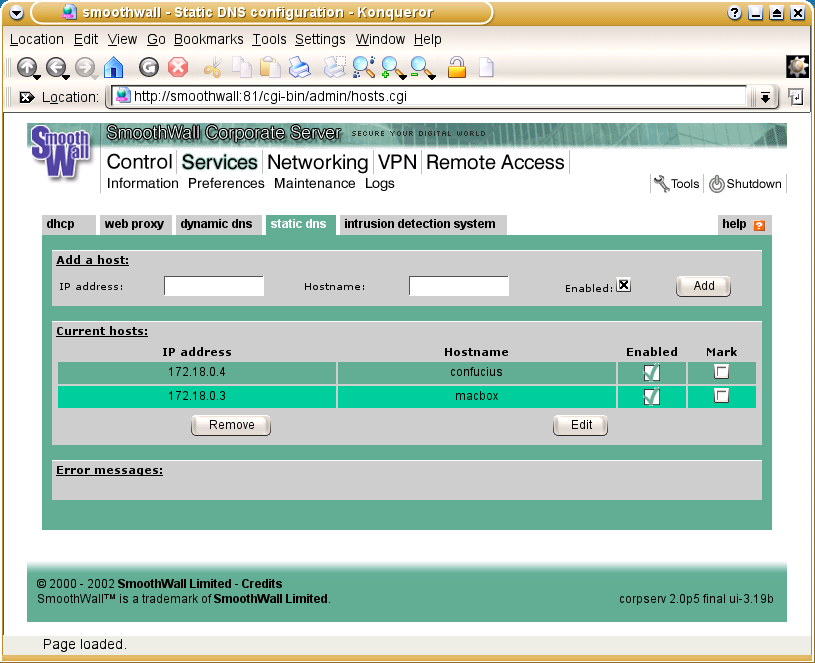
The 'Services' section should also prove familiar. Here you can configure SmoothWall's DHCP server, web proxy and DNS cache. The DHCP section is straightforward and lets you add blocks of IP addresses for dynamic assignment and to configure static IPs based on MAC address. The 'Web proxy' page is for simple configuration of Squid. Interesting features here include forwarding to a remote proxy and 'transparent' operation. The latter enables caching on all web connection via the firewall, not just those via the proxy port, and eases the setting up of client machines. 'Static DNS' is where you add static IP numbers and their host names to SmoothWall's DNS cache, and 'Dynamic DNS' provides automatic support for various dynamic DNS services - such as no-ip.com and dyndns.org - which let you assign a world-visible host and domain name to your firewall when it's on a dynamic IP address. The final page is for the intrusion detection system, Snort, and this just turns it on or off.
After your firewall is configured, the pages that most users will spend their time viewing are in the 'Information' and 'Logs' sections. The former provides status information and detailed traffic graphs and statistics. These display the traffic on each of the interfaces and VPN traffic separately. The 'Logs' section lets you monitor the behaviour and security of your firewall in more detail. As well as a general activity log, this provides access to the web proxy, firewall and intrusion detection logs. The firewall log displays IP packets dropped by the firewall (you cannot configure which packets are logged, though) and provides a look-up function to do a reverse look-up on the source address of any dropped packets. All the various logs can be saved out as files for archival or analysis purposes, but SmoothWall doesn't support the automated external storage of logs, emailing of logs, or any kind of alarm system. The upshot is, you do have to monitor these pages regularly to maintain the health of your firewall.
The other aspect of maintenance is ensuring your software is up-to-date. SmoothWall checks on line for available updates, and any update announcements can be viewed in the maintenance section of the web interface. Using this interface, you can download updates to your admin host, and then upload them to your firewall where they will be installed. Simple enough, if a rather roundabout way of doing it. Add-on modules can be installed in a similar manner.
Conclusion
SmoothWall Corporate Server builds on the strengths of the free SmoothWall to create a more scalable product. The increased hardware support, the more flexible networking tools - such as the support for multiple sub-nets - and the modular, extensible architecture will certainly widen its appeal to larger businesses. I have two main worries. One is that SmoothWall is based on a 2.2 kernel and so support for newer hardware isn't as good as it might have been had it had been based on a 2.4 kernel (I know the system was originally meant for redundant hardware, but scaling up to larger networks requires more horsepower, after all.) My second concern is the lack of any automated tools for firewall monitoring. It should really be able to email intrusion detection alerts to an administrator, rather than requiring somebody to constantly monitor log files. Having said all this, SmoothWall Corporate Server does what it sets out to do and, at this price, is an outrageously good bargain.
Verdict
| Ease of use: | 8/10 |
| Performance: | 9/10 |
| Features: | 8/10 |
| Value for money: | 9/10 |
| As simple to use as the original SmoothWall, but those extra features and scalability means that it can tackle bigger networks. A bargain. | |
| Rating: | 9/10 |